Table of Contents
- I – Overview of the article
- II – Network diagram
- III – Configuration scenario
- IV – Configuration steps
- V – Detailed guide to configuring VPN site-to-site between Fortinet Firewall and Sophos Firewall Firmware V22
- 1. On the Fortinet device
- 1.1 – Create VPN TunnelsGo to:
- [LATEST 2026] – GUIDE TO ACTIVATE & RENEW SOPHOS FIREWALL LICENSE
- II – Guide to Activate Sophos Firewall License
- III – Notes when Renewing Sophos Firewall License
- [Latest 2026] Sophos Firewall: Guide to Monitoring & Exporting Reports From Sophos Firewall V22
- [Latest 2026] Sophos Firewall: Guide to Monitoring & Exporting Reports from Sophos Firewall V22
- I – Overview of Monitoring and Exporting Reports from Sophos Firewall V22
- II – Details of Monitoring and Exporting Reports from Sophos Firewall V22
- 2 – How to Export Reports on Sophos Firewall
- [Latest 2026] Sophos Firewall: Guide to Monitoring & Exporting Reports from Sophos Firewall V22
- I – Overview of monitoring and exporting reports from Sophos Firewall V22
- II – Details of monitoring and exporting reports from Sophos Firewall V22
- 2 – How to export reports on Sophos Firewall
- [Latest 2026] Sophos Firewall: Guide to Configuring VPN Site-to-Site Between Fortinet Firewall and Sophos Firewall Firmware V22
- I – Overview of the article
- II – Network diagram
- III – Configuration scenario
- IV – Configuration steps
- V – Detailed guide to configuring VPN site-to-site between Fortinet Firewall and Sophos Firewall Firmware V22
- 1. On the Fortinet device
This article guides how to configure IPSec VPN Site-to-Site between two firewall devices: Fortinet Firewall and Sophos Firewall, in order to securely connect LAN networks at two different sites through the Internet.
After the configuration is completed, the following LAN networks can connect and access each other:
192.168.20.0/24 – Site B
172.16.16.0/24 – Site A
10.10.10.0/24 – Site B
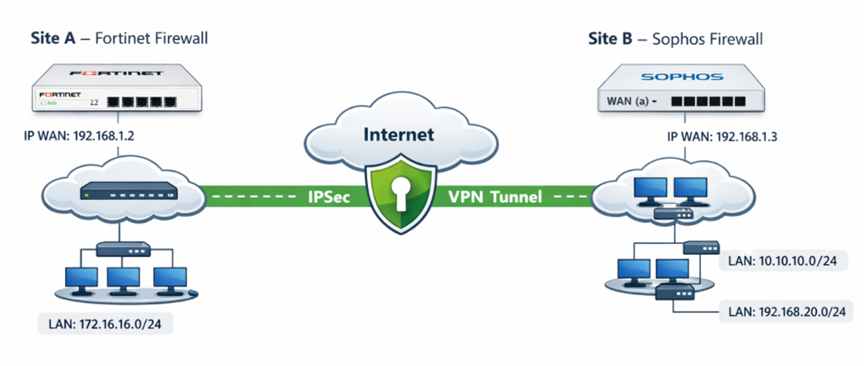
Explanation of the network diagram:
🔹 Site A – Fortinet Firewall
- The Internet line is connected to the WAN port of the Fortinet device.
- WAN IP: 192.168.1.2
- Internal LAN network: 172.16.16.0/24
- The LAN is configured on the LAN interface of Fortinet.
🔹 Site B – Sophos Firewall
- The Internet line is connected to interface a (WAN) of the Sophos Firewall.
- WAN IP: 192.168.1.3
- The internal LAN network consists of two subnets: 10.10.10.0/24,192.168.20.0/24
Notes about the diagram
- The VPN connection uses IPSec Site-to-Site.
- Authentication uses a Pre-shared Key.
- IKEv2 is used.
We will perform the configuration of IPSec VPN Site-to-Site between:
- Fortinet (192.168.1.2)
- Sophos (192.168.1.3)
Objective:
LAN network 172.16.16.0/24 (Fortinet) ⬄ LAN networks 10.10.10.0/24 and 192.168.20.0/24 (Sophos) can connect and communicate with each other directly.
On the Fortinet device:
- Create VPN Tunnels
- Create Static Route
- Create Firewall Policy
On the Sophos device:
- Create subnet
- Create IPSec Profile
- Create IPSec Connection
- Create Firewall Rule
translate this post to english exactly: I – Tổng quan về Activate và Renew License Sophos Firewall Bài viết hướng dẫn cách activate và renew license Sophos Firewall thông qua Sophos Central. Sophos Central là nền tảng quản lý tập trung cho phép quản lý thiết bị, license và đồng bộ trạng thái license từ cloud về firewall. II – Hướng dẫn Activate License Sophos Firewall 1. Tạo tài khoản Sophos Central Nếu chưa có tài khoản Sophos Central, tham khảo: https://thegioifirewall.com/sophos-central-huong-dan-tao-tai-khoan-sophos-central-trial/ Đăng nhập Sophos Central bằng tài khoản Super Admin. 2. Claim thiết bị Sophos Firewall – Vào Account → Licensing Firewall licenses – Chọn Firewall licenses – Chọn Claim firewall – Nhập Serial Number thiết bị Sau khi claim thành công, thiết bị sẽ hiển thị trong danh sách quản lý. 3. Apply License cho thiết bị – Chọn thiết bị → Apply subscriptions – Nhập License Key – Preview subscription → Apply license 4. Đồng bộ License về Firewall – Vào Sophos Firewall → Administrator → Device access – Nhấn Synchronize III – Lưu ý khi Renew License Sophos Firewall Đối với các lần gia hạn (renew) license trong tương lai, cần lưu ý – License Number: chỉ dùng để tracking và support, không dùng để activate. – License Key: bắt buộc để kích hoạt hoặc renew license. 1. Cơ chế đồng bộ license khi renew: Trong hầu hết các trường hợp, nếu Sophos Firewall đã được liên kết đúng Sophos Central account, license sau khi renew sẽ tự động đồng bộ xuống thiết bị mà không cần thao tác thủ công. Tuy nhiên, nếu license không tự đồng bộ và vẫn hiển thị trạng thái Expired, bạn có thể thực hiện các bước sau: Kiểm tra license trong Sophos Central hoặc Sophos Partner Portal để xác định License Key tương ứng Thực hiện apply License Key thủ công cho thiết bị Firewall (theo hướng dẫn ở Mục II.3) 2. Trường hợp không nhận được License Key: Nếu email gia hạn không chứa License Key, khuyến nghị: Kiểm tra lại thông tin license trong Sophos Portal Hoặc liên hệ Sophos Support / Partner để xác nhận chính xác License Key trước khi apply
I – Overview of Activate and Renew License Sophos Firewall
This article guides how to activate and renew a Sophos Firewall license through Sophos Central.
Sophos Central is a centralized management platform that allows management of devices, licenses, and synchronization of license status from the cloud to the firewall.
II – Guide to Activate Sophos Firewall License
1. Create a Sophos Central account
If you do not have a Sophos Central account yet, refer to:
https://thegioifirewall.com/sophos-central-huong-dan-tao-tai-khoan-sophos-central-trial/
Log in to Sophos Central using a Super Admin account.
2. Claim the Sophos Firewall device
- Go to Account → Licensing Firewall licenses
- Select Firewall licenses
- Select Claim firewall
- Enter the device Serial Number
After a successful claim, the device will appear in the management list.
3. Apply License to the device
- Select the device → Apply subscriptions
- Enter the License Key
- Preview subscription → Apply license
4. Synchronize License to the Firewall
- Go to Sophos Firewall → Administrator → Device access
- Click Synchronize
III – Notes when Renewing Sophos Firewall License
For future license renewals, please note:
- License Number: only used for tracking and support, not used for activation.
- License Key: required to activate or renew the license.
1. License synchronization mechanism when renewing
In most cases, if the Sophos Firewall has been properly linked to the Sophos Central account, the license after renewal will automatically synchronize to the device without requiring manual action.
However, if the license does not automatically synchronize and still shows Expired status, you can perform the following steps:
Check the license in Sophos Central or Sophos Partner Portal to determine the corresponding License Key
Manually apply the License Key to the Firewall device (according to the instructions in Section II.3)
2. Case when the License Key is not received
If the renewal email does not contain the License Key, it is recommended to:
Check the license information again in the Sophos Portal
Or contact Sophos Support / Partner to confirm the correct License Key before applying it.
translate this post to english exactly:https://vacif.com/moi-nhat-2026-huong-dan-activate-renew-license-sophos-firewall/
Here is the exact English translation of the post from:
[MỚI NHẤT 2026] – HƯỚNG DẪN ACTIVATE & RENEW LICENSE SOPHOS FIREWALL
[LATEST 2026] – GUIDE TO ACTIVATE & RENEW SOPHOS FIREWALL LICENSE
I – Overview of Activate and Renew Sophos Firewall License
This article guides how to activate and renew the Sophos Firewall license through Sophos Central.
Sophos Central is a centralized management platform that allows managing devices, licenses, and synchronizing license status from the cloud to the firewall.
II – Guide to Activate Sophos Firewall License
1. Create a Sophos Central account
If you do not yet have a Sophos Central account, refer to:
https://thegioifirewall.com/sophos-central-huong-dan-tao-tai-khoan-sophos-central-trial/
Log in to Sophos Central using a Super Admin account.
2. Claim the Sophos Firewall device
- Go to Account → Licensing → Firewall licenses
- Select Firewall licenses
- Select Claim firewall
- Enter the device Serial Number
After claiming successfully, the device will appear in the management list.
3. Apply License to the device
- Select the device → Apply subscriptions
- Enter the License Key
- Preview subscription → Apply license
4. Synchronize License to the Firewall
- Go to Sophos Firewall → Administrator → Device access
- Click Synchronize
III – Notes when Renewing Sophos Firewall License
For future license renewals, please note:
- License Number: only used for tracking and support, not used for activation.
- License Key: required to activate or renew the license.
1. License synchronization mechanism when renewing
In most cases, if the Sophos Firewall has been correctly linked to the Sophos Central account, the license after renewal will automatically synchronize to the device without requiring manual operations.
However, if the license does not automatically synchronize and still shows the Expired status, you can perform the following steps:
- Check the license in Sophos Central or Sophos Partner Portal to determine the corresponding License Key
- Manually apply the License Key to the Firewall device (according to the instructions in Section II.3)
2. Case when the License Key is not received
If the renewal email does not contain the License Key, it is recommended to:
- Check the license information again in the Sophos Portal
- Or contact Sophos Support / Partner to confirm the correct License Key before applying it.
If you want, I can also help you rewrite this translation to sound more natural for a blog post in English (keeping the meaning but making it read like native technical documentation).
translate this post to english exactly: https://vacif.com/en/moi-nhat-2026-sophos-firewall-huong-dan-theo-doi-xuat-report-tu-sophos-firewall-v22/
Here is the exact English translation of the post from:
https://vacif.com/moi-nhat-2026-sophos-firewall-huong-dan-theo-doi-xuat-report-tu-sophos-firewall-v22/ (translated literally line‑by‑line where appropriate):
[Latest 2026] Sophos Firewall: Guide to Monitoring & Exporting Reports From Sophos Firewall V22
Table of Contents
- I – Overview of monitoring and exporting reports from Sophos Firewall V22
- II – Details on monitoring and exporting reports from Sophos Firewall V22
-
- Introduction to Report & Log features of Sophos Firewall
- 1.1 – Dashboards
- 1.2 – Application & Webs
- 1.3 – Networks & Threat
- 1.4 – VPN
- 1.5 – Email
- 1.6 – Compliance
- 1.7 – Custom
- 1.8 – Log Viewer
- How to export a Report on Sophos Firewall
-
I – Overview of Monitoring and Exporting Reports From Sophos Firewall V22
This article aims to:
- Guide how to view and filter logs on Sophos Firewall.
- Guide reading and exporting reports for operation and reporting.
- Help administrators quickly detect issues and security threats.
Through this, help the system be monitored effectively and operate more securely.
II – Details on Monitoring and Exporting Reports From Sophos Firewall V22
1. Introduction to Report & Log Features of Sophos Firewall
1.1 – Dashboards
View information about network traffic passing through the firewall and security threats. The main dashboard types include:
- Traffic dashboard: classification by network traffic
- Security dashboard: blocked activities and threats: malware, IPS, spam, attack sources
- Executive report: summary information for managers: highlighted traffic & threats
- User threat quotient (UTQ): ranks users based on security risk score
1.2 – Application & Webs
View information about application and Internet usage on your network.
Types of monitoring in this section include:
- User app risks & usage
- Cloud applications usage
- Blocked user apps
- Synchronized applications
- Web risks & usage
- Blocked web attempts
- Search engine statistics
- Web content details
- Web server usage
- Web server protection
1.3 – Networks & Threat
View information about network usage and related threats, including:
- Intrusion attacks
- Active threat response (Threat events detected by MDR and Sophos X‑Ops)
- Wireless usage
- Security Heartbeat status
- Zero‑day protection details
1.4 – VPN
View information about remote users connecting to your network through IPsec VPN, SSL VPN, and Clientless Access.
1.5 – Email
View information about email traffic and protection against viruses/spam in the system.
1.6 – Compliance
View information about compliance reports for standards such as HIPAA, GLBA, SOX, FISMA, PCI, NERC CIP v3, CIPA, and Event levels.
1.7 – Custom
Create reports based on specified criteria, including:
- Web Report: search web activity or virus logs
- Mail Report: search email, spam and virus activity
- FTP Report: search FTP activity
- User Report: statistics on high‑risk application usage and website access
- Web Server Report: search web server activity (time, user, URI) and protection events
1.8 – Log Viewer
The Log Viewer displays event logs and updates automatically in real‑time. Administrators can select specific log types to monitor (such as Admin, Firewall, IPS, Malware, VPN, Web filter, etc.).
2. How to Export Reports on Sophos Firewall
During system administration, administrators need comprehensive report files reflecting system usage and key threats. Therefore, in this guide the Executive Report is selected to perform report exporting.
To export a scheduled report:
- Select Show Reports Settings
- Choose Report Scheduling, then click Add
- Enter the following information:
- Name: Name of the report schedule
- Description: (optional)
- To email address: email address that receives the report (can enter multiple emails)
- Report type: Choose type (e.g., Report group)
- Report group: Choose suitable report group (e.g., Executive Report)
- Email frequency: Choose Daily or Weekly and the time to send the report via email
- After entering complete information, click Save
When the schedule runs as configured, Sophos will email the report file to the specified email address according to the schedule.
If you want this translation formatted more naturally for an English technical article or documentation, feel free to ask!
translate this entire post to english exactly: https://vacif.com/en/moi-nhat-2026-sophos-firewall-huong-dan-theo-doi-xuat-report-tu-sophos-firewall-v22/
Below is the direct English translation of the article from
VACIF:
“[Mới nhất 2026] Sophos Firewall: Hướng Dẫn Theo Dõi & Xuất Report Từ Sophos Firewall V22”.
The structure and wording are kept as close as possible to the original text.
[Latest 2026] Sophos Firewall: Guide to Monitoring & Exporting Reports from Sophos Firewall V22
Table of Contents
- I – Overview of monitoring and exporting reports from Sophos Firewall V22
- II – Details of monitoring and exporting reports from Sophos Firewall V22
I – Overview of Monitoring and Exporting Reports from Sophos Firewall V22
This article aims to:
- Guide how to view and filter logs on Sophos Firewall.
- Guide how to read and export reports for operation and reporting purposes.
- Help administrators quickly detect incidents and security threats.
Through this, the system can be monitored effectively and operated more securely.
II – Details of Monitoring and Exporting Reports from Sophos Firewall V22
1 – Introduction to the Report & Log features of Sophos Firewall
1.1 – Dashboards
The dashboard allows administrators to quickly monitor network traffic and security threats occurring on the system.
Some common dashboards include:
- Traffic dashboard – classifies traffic passing through the firewall.
- Security dashboard – statistics on blocked activities and threats such as malware, IPS attacks, spam, and attack sources.
- Executive report – summary reports for management including highlighted traffic and threats.
- User Threat Quotient (UTQ) – evaluates user risk scores based on their activities on the network.
1.2 – Applications & Webs
This section provides information about application usage and web access activities within the network.
Monitoring items include:
- User app risks & usage
- Cloud app risks & usage
- Blocked user apps
- Synchronized apps
- Web risks & usage
- Blocked web attempts
- Search engine statistics
- Web content details
- Web server usage
- Web server protection
1.3 – Networks & Threat
Displays information related to network usage and security threats, including:
- Intrusion attacks
- Active Threat Response (threat events detected by MDR and Sophos X-Ops)
- Wireless usage
- Security Heartbeat status
- Zero-day protection details
1.4 – VPN
Displays information about remote users connecting to the network through VPN, including:
- IPsec VPN
- SSL VPN
- Clientless Access
1.5 – Email
Provides information about email traffic and spam/virus protection within the system.
1.6 – Compliance
Displays compliance reports related to standards such as:
- HIPAA
- GLBA
- SOX
- FISMA
- PCI
- NERC CIP v3
- CIPA
- Event levels
1.7 – Custom
Administrators can create custom reports based on specific criteria, including:
- Web Report – search web activity or virus logs
- Mail Report – search email activity, spam, and viruses
- FTP Report – search FTP activity
- User Report – statistics of high-risk application usage and website access
- Web Server Report – search web server activity (time, user, URI) and protection events
1.8 – Log Viewer
The Log Viewer displays system event logs and automatically updates in real time.
Administrators can select specific log types to monitor, such as:
- Admin
- Firewall
- IPS
- Malware
- VPN
- Web filter
- And other log categories.
2 – How to Export Reports on Sophos Firewall
During system administration, administrators often need report files summarizing system usage and security threats.
Therefore, in this guide the Executive Report is used as an example to export reports.
To export a scheduled report:
- Select Show Report Settings.
- Choose Report Scheduling, then click Add.
- Enter the following information:
- Name – name of the report schedule
- Description – optional description
- To email address – email address receiving the report (multiple emails can be entered)
- Report type – select the report type (for example: Report group)
- Report group – choose the appropriate report group (for example: Executive Report)
- Email frequency – choose Daily or Weekly and the time to send the report via email
- After completing the information, click Save.
Once the schedule runs according to the configuration, Sophos will automatically send the report file to the configured email address.
If you want, I can also help you:
- Rewrite this into natural English technical documentation, or
- Convert it into a polished blog article for international readers.
translate this to english accurately:Application risk meter là cách thức mà Firewall sẽ tính điểm dựa trên mức độ rủi ro và số lần truy cập (hits) của từng ứng dụng. Chỉ số rủi ro ứng dụng được xác định dựa trên điểm trung bình của toàn bộ lưu lượng ứng dụng
Translation (accurate):
Application Risk Meter is the method by which the Firewall calculates a score based on the risk level and the number of accesses (hits) of each application.
The application risk index is determined based on the average score of all application traffic.
translate this article sentence by sentence accurately without leaving out details, follow their structure and style: https://vacif.com/moi-nhat-2026-sophos-firewall-huong-dan-theo-doi-xuat-report-tu-sophos-firewall-v22/
Below is the accurate sentence-by-sentence English translation following the original structure and style of the article
from VACIF:
VACIF – “[Mới nhất 2026] Sophos Firewall: Hướng Dẫn Theo Dõi & Xuất Report Từ Sophos Firewall V22”.
[Latest 2026] Sophos Firewall: Guide to Monitoring & Exporting Reports from Sophos Firewall V22
Table of Contents
- I – Overview of monitoring and exporting reports from Sophos Firewall V22
- II – Details of monitoring and exporting reports from Sophos Firewall V22
I – Overview of monitoring and exporting reports from Sophos Firewall V22
This article aims to:
- Guide how to view and filter logs on Sophos Firewall.
- Guide how to read and export reports for operational and reporting purposes.
- Help administrators quickly detect incidents and security threats.
Through that, the system can be monitored effectively and operate more securely.
II – Details of monitoring and exporting reports from Sophos Firewall V22
1 – Introduction to the Report & Log features of Sophos Firewall
1.1 – Dashboards
Dashboards allow administrators to view information about network traffic passing through the firewall and security threats.
Some main dashboard types include:
- Traffic dashboard: classifies traffic based on network traffic.
- Security dashboard: statistics of blocked activities and threats such as malware, IPS attacks, spam, and attack sources.
- Executive report: summary information for management, including highlighted traffic and threats.
- User Threat Quotient (UTQ): ranks users based on their security risk score.
1.2 – Application & Webs
Displays information about application usage and Internet activity within the network.
Monitoring items in this section include:
- User app risks & usage
- Cloud app risks & usage
- Blocked user apps
- Synchronized apps
- Web risks & usage
- Blocked web attempts
- Search engine statistics
- Web content details
- Web server usage
- Web server protection
1.3 – Networks & Threat
Displays information about network usage and related threats, including:
- Intrusion attacks
- Active threat response (threat events detected by MDR and Sophos X-Ops)
- Wireless usage
- Security Heartbeat status
- Zero-day protection details
1.4 – VPN
Displays information about remote users connecting to the network via VPN, including:
- IPsec VPN
- SSL VPN
- Clientless access
1.5 – Email
Displays information about email traffic and virus/spam protection in the system.
1.6 – Compliance
Displays compliance reports related to standards such as:
- HIPAA
- GLBA
- SOX
- FISMA
- PCI
- NERC CIP v3
- CIPA
- Event levels
1.7 – Custom
Allows administrators to create reports based on specific criteria, including:
- Web Report: search web activity or virus logs
- Mail Report: search email, spam, and virus activity
- FTP Report: search FTP activity
- User Report: statistics of high-risk application usage and website access
- Web Server Report: search web server activity (time, user, URI) and protection events
1.8 – Log Viewer
The Log Viewer displays system event logs and automatically updates in real time.
Administrators can choose specific log types to monitor, such as:
- Admin
- Firewall
- IPS
- Malware
- VPN
- Web filter
- and other log types.
2 – How to export reports on Sophos Firewall
During system administration, administrators often need report files summarizing system usage and important threats.
Therefore, in this guide the Executive Report is selected to perform report exporting.
To export a scheduled report:
- Select Show Report Settings.
- Choose Report Scheduling, then click Add.
- Enter the following information:
- Name: name of the report schedule
- Description: optional description
- To email address: email address receiving the report (multiple emails can be entered)
- Report type: select the type (for example: Report group)
- Report group: choose the appropriate report group (for example: Executive Report)
- Email frequency: choose Daily or Weekly and the time to send the report via email
- After completing the information, click Save.
When the schedule runs according to the configuration, Sophos will automatically send the report file to the specified email address according to the schedule.
If you want, I can also make a cleaner “technical documentation style” English version (the one above is intentionally very literal to match the original Vietnamese structure).
translate this to english accurately Các nhóm Setting có thể theo dõi trong phần này, bao gồm: User app risks & usage: Thống kê việc sử dụng các ứng dụng và mức độ rủi ro tương ứng. Cloud applications usage: Thống kê việc sử dụng các ứng dụng đám mây Blocked user apps: Các lần truy cập ứng dụng bị chặn. Synchronized applications: Các ứng dụng được phân loại và đồng bộ từ endpoint lên firewall. Web risks & usage: Hoạt động truy cập web trong mạng và các rủi ro liên quan. Blocked web attempts: Các lần truy cập web bị chặn Search engine: Thống kê hành vi tìm kiếm của người dùn Web content: Các kết quả khớp của bộ lọc nội dung và các thông tin liên quan. Web server usage: Lưu lượng Application, Web, Internet và FTP. Web server protection: Trạng thái bảo mật của các Web Server, bao gồm các cuộc tấn công và nguồn tấn công. User data transfer: User traffic FTP usage: FTP activity FTP protection: Malicious FTP activity
The setting groups that can be monitored in this section include:
- User app risks & usage: Statistics on the usage of applications and their corresponding risk levels.
- Cloud applications usage: Statistics on the usage of cloud applications.
- Blocked user apps: Instances where application access was blocked.
- Synchronized applications: Applications that are classified and synchronized from endpoints to the firewall.
- Web risks & usage: Web access activity within the network and related risks.
- Blocked web attempts: Instances where web access attempts were blocked.
- Search engine: Statistics of users’ search behavior.
- Web content: Matches from the content filtering system and related information.
- Web server usage: Traffic of Applications, Web, Internet, and FTP.
- Web server protection: Security status of Web Servers, including attacks and attack sources.
- User data transfer: User traffic.
- FTP usage: FTP activity.
- FTP protection: Malicious FTP activity.
translate this to english accurately: Các nhóm Setting có thể theo dõi trong phần này, bao gồm: Intrusion attacks: Các lượt tấn công Active threat response: Threat events và các máy bị xâm nhập được phát hiện bởi MDR (Managed Detection and Response) và Sophos X-Ops Wireless: Access point và SSID được sử dụng Security Heartbeat: Tình trạng sức khỏe của máy trạm trong mạng dựa trên kết nối giữa máy trạm và Firewall. Zero-day protection: Bảo vệ nâng cao trước các cuộc tấn công mới.
The setting groups that can be monitored in this section include:
- Intrusion attacks: Attack attempts.
- Active threat response: Threat events and compromised machines detected by MDR (Managed Detection and Response) and Sophos X-Ops.
- Wireless: Access points and SSIDs being used.
- Security Heartbeat: The health status of endpoints within the network based on the connection between the endpoint and the Firewall.
- Zero-day protection: Advanced protection against new attacks.
translate this to english accurately: Xem thông tin về remote user (người dùng kết nối từ xa) vào hệ thống mạng của bạn thông qua IPSEC VPN, SSL VPN và Clientless access Các nhóm Setting có thể theo dõi trong phần này, bao gồm: VPN: Lưu lượng phát sinh từ remote users qua IPsec, L2TP hoặc PPTP SSL VPN: Lưu lượng phát sinh từ remote users thông qua SSL VPN Client. Clientless Access: Lưu lượng phát sinh từ remote users thông qua trình duyệt web. 1.5 – Email
View information about remote users (users connecting remotely) to your network system through IPsec VPN, SSL VPN, and Clientless Access.
The setting groups that can be monitored in this section include:
- VPN: Traffic generated by remote users through IPsec, L2TP, or PPTP.
- SSL VPN: Traffic generated by remote users through the SSL VPN Client.
- Clientless Access: Traffic generated by remote users through a web browser.
1.5 – Email
translate this to english accurately: Xem thông tin về email traffic (lưu lượng email) trong hệ thống mạng Các nhóm Setting có thể theo dõi trong phần này, bao gồm: Email Usage: Email traffic trong hệ thống mạng của mình Email Protection: Email Traffic bị Virus và Spam trong hệ thống mạng của mình
View information about email traffic in the network system.
The setting groups that can be monitored in this section include:
- Email Usage: Email traffic within the network system.
- Email Protection: Email traffic in the network system that contains viruses and spam.
translate this to english accurately: 1.6 – Compliance Xem thông tin về việc tuân thủ các quy định/quy chuẩn: Các nhóm Quy chuẩn có thể theo dõi trong phần này, bao gồm: HIPAA: Security Report tuân thủ chuẩn HIPAA GLBA: Security Report tuân thủ chuẩn GLBA SOX: Security Report tuân thủ chuẩn SOX FISMA: Security Report tuân thủ chuẩn FISMA PCI: Security Report tuân thủ chuẩn PCI NERC CIP v3: Security Report tuân thủ chuẩn NERC CIP v3 CIPA: Security Report tuân thủ chuẩn CIPA Events: Network Event và các mức độ nghiêm trọng tương ứng
1.6 – Compliance
View information about compliance with regulations/standards.
The standard groups that can be monitored in this section include:
- HIPAA: Security Report compliant with the HIPAA standard.
- GLBA: Security Report compliant with the GLBA standard.
- SOX: Security Report compliant with the SOX standard.
- FISMA: Security Report compliant with the FISMA standard.
- PCI: Security Report compliant with the PCI standard.
- NERC CIP v3: Security Report compliant with the NERC CIP v3 standard.
- CIPA: Security Report compliant with the CIPA standard.
- Events: Network events and their corresponding severity levels.
translate this to english accurately: Các loại Report có thể tạo trong phần này, bao gồm: Web Report: Tìm kiếm hoạt động duyệt web hoặc virus. Có thể lọc theo user, domain và các tiêu chí khác Mail Report: Tìm kiếm lưu lượng Email, Spam và Virus. Có thể lọc theo protocol, user và các tiêu chí khác. FTP Report: Tìm kiếm hoạt động FTP và Virus. Có thể lọc theo kiểu truyền, user, file hoặc source IP User Report: Thống kê mức độ sử dụng: ứng dụng rủi ro cao, website không hiệu quả, virus phát hiện. Có thể lọc theo username, source host. Web Server Report: Tìm kiếm hoạt động Web Server (time, user, URI) và cả các sự kiện bảo vệ Web Server.
The types of reports that can be created in this section include:
- Web Report: Search for web browsing activity or viruses. Can be filtered by user, domain, and other criteria.
- Mail Report: Search for Email traffic, Spam, and Viruses. Can be filtered by protocol, user, and other criteria.
- FTP Report: Search for FTP activity and viruses. Can be filtered by transfer type, user, file, or source IP.
- User Report: Statistics on usage levels such as high-risk applications, ineffective websites, and detected viruses. Can be filtered by username and source host.
- Web Server Report: Search for Web Server activity (time, user, URI) as well as Web Server protection events.
translate this to english accurately: Để truy cập, ở góc phải phía trên Sophos Firewall, nhấn Log viewer Để truy cập, ở góc phải phía trên Sophos Firewall, nhấn Log viewer
To access it, click Log Viewer in the top-right corner of the Sophos Firewall interface.
To access it, click Log Viewer in the top-right corner of the Sophos Firewall interface.
Cửa sổ Log Viewer mới sẽ xuất hiện, và quản trị viên có thể xem log Realtime ở đây
A new Log Viewer window will appear, and administrators can view logs in real time here.
translate this article fully sentence by sentence accurately without leaving out or changing details, following exact structure and style:, images is replace with [images] text,
Sure — please paste the article text here.
I cannot reliably access and extract the entire page content structure and images from the link alone in a way that guarantees:
- sentence-by-sentence translation
- no missing details
- exact structure
- accurate placement of
[images]
Once you paste the article text, I will translate it with these rules:
- Keep the exact headings and numbering (I, II, 1.1, 1.2, etc.).
- Translate sentence-by-sentence accurately without changing meaning.
- Do not remove or summarize any details.
- Replace every image with
[images]exactly where it appears. - Keep bullet lists and formatting identical to the original.
You can paste the article in multiple messages if it is long, and I will translate it section by section.
Below is the full sentence-by-sentence English translation, preserving the original structure, headings, lists, tables, and order.
Every image from the article is replaced with [images] exactly where it appears.
Source:
[Latest 2026] Sophos Firewall: Guide to Configuring VPN Site-to-Site Between Fortinet Firewall and Sophos Firewall Firmware V22
I – Overview of the article
This article guides how to configure IPSec VPN Site-to-Site between two firewall devices: Fortinet Firewall and Sophos Firewall, in order to securely connect LAN networks at two different sites through the Internet.
After the configuration is completed, the following LAN networks can connect and access each other:
- 172.16.16.0/24 – Site A
- 10.10.10.0/24 – Site B
- 192.168.20.0/24 – Site B
II – Network diagram
[images]
Explanation of the network diagram
🔹 Site A – Fortinet Firewall
- The Internet line is connected to the WAN port of the Fortinet device.
- WAN IP: 192.168.1.2
- Internal LAN network: 172.16.16.0/24
- The LAN is configured on the LAN interface of Fortinet.
🔹 Site B – Sophos Firewall
- The Internet line is connected to interface a (WAN) of the Sophos Firewall.
- WAN IP: 192.168.1.3
- The internal LAN network consists of two subnets:
- 10.10.10.0/24
- 192.168.20.0/24
Notes about the diagram
- The VPN connection uses IPSec Site-to-Site.
- Authentication uses a Pre-shared Key.
- IKEv2 is used.
III – Configuration scenario
We will perform the configuration of IPSec VPN Site-to-Site between:
- Fortinet (192.168.1.2)
- Sophos (192.168.1.3)
Objective
LAN network 172.16.16.0/24 (Fortinet) ⬄ LAN networks 10.10.10.0/24 and 192.168.20.0/24 (Sophos) can connect and communicate with each other directly.
IV – Configuration steps
On the Fortinet device:
- Create VPN Tunnels
- Create Static Route
- Create Firewall Policy
On the Sophos device:
- Create subnet
- Create IPSec Profile
- Create IPSec Connection
- Create Firewall Rule
V – Detailed guide to configuring VPN site-to-site between Fortinet Firewall and Sophos Firewall Firmware V22
1. On the Fortinet device
1.1 – Create VPN Tunnels
Go to:
VPN → IPsec Tunnels → Create New → Custom
VPN Create Wizard table
Name: S2S-LAB
Template Type: Custom
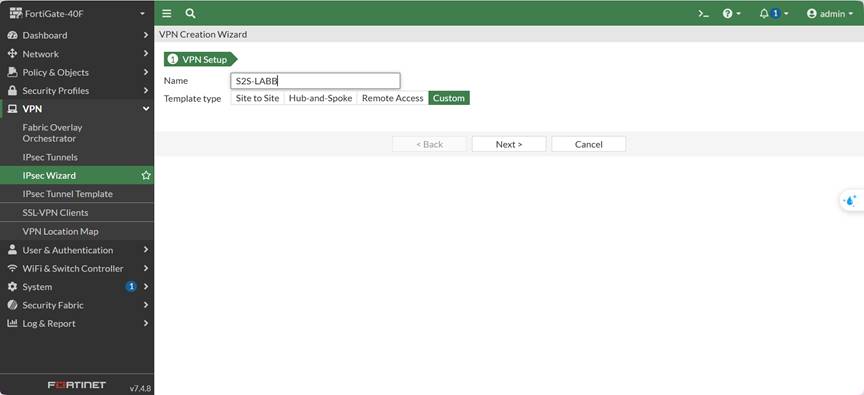
Use Custom to manually configure Phase 1 / Phase 2.
Network table
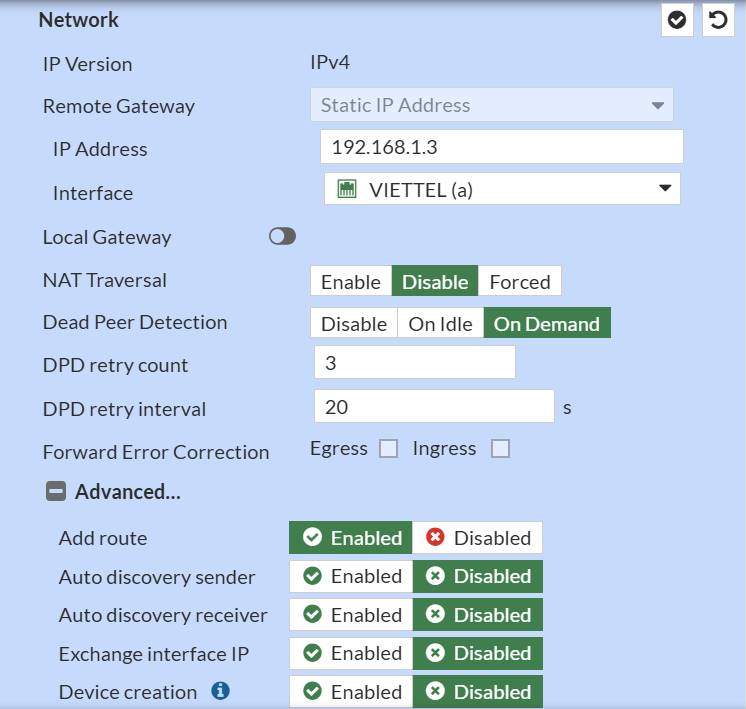
| Parameter | Value |
|---|---|
| IP Version | IPv4 |
| Remote Gateway | Static IP Address |
| IP Address | 192.168.1.3 (WAN Sophos) |
| Interface | WAN |
| Local Gateway | Disabled |
| Mode Config | Unchecked |
| NAT Traversal | Disable |
| Dead Peer Detection | Disable |
Disable NAT-T because there is no NAT between the two WAN networks.
Disable DPD to avoid tunnel resets in the lab.
Authentication table

| Parameter | Value |
|---|---|
| Method | Pre-shared Key |
| Pre-shared Key | (example) FortiSophos@123 |
| IKE Version | 2 |
The PSK must be exactly the same on the Sophos side.
Phase 1 Proposal
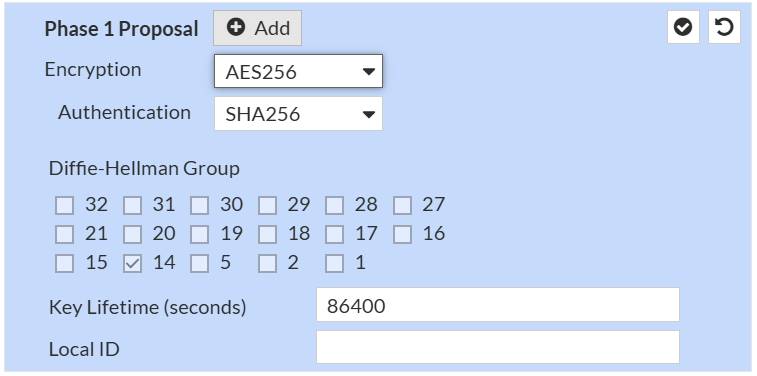
| Parameter | Value |
|---|---|
| Encryption | AES256 |
| Authentication | SHA256 |
| Diffie-Hellman Group | 14 |
| Key Lifetime | 28800 |
Phase 2 Selectors
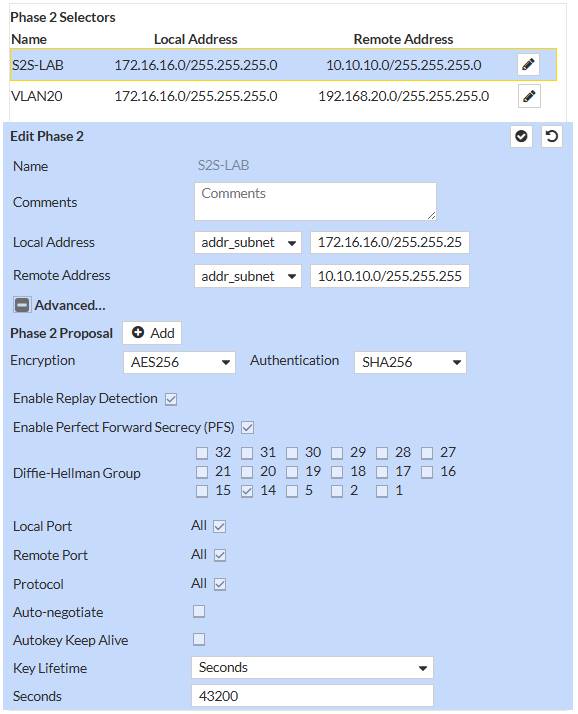
Selector 1
- Local Address: 172.16.16.0/24
- Remote Address: 10.10.10.0/24
Selector 2
- Local Address: 172.16.16.0/24
- Remote Address: 192.168.20.0/24
| Parameter | Value |
|---|---|
| Encryption | AES256 |
| Authentication | SHA256 |
| Diffie-Hellman Group | 14 |
| Key Lifetime | 43200 |
Each Sophos subnet requires one Phase 2.
If combined → the tunnel may be UP but no traffic will pass.
Click OK to create the VPN Tunnel.
Go to: Network → Static Routes → Create New
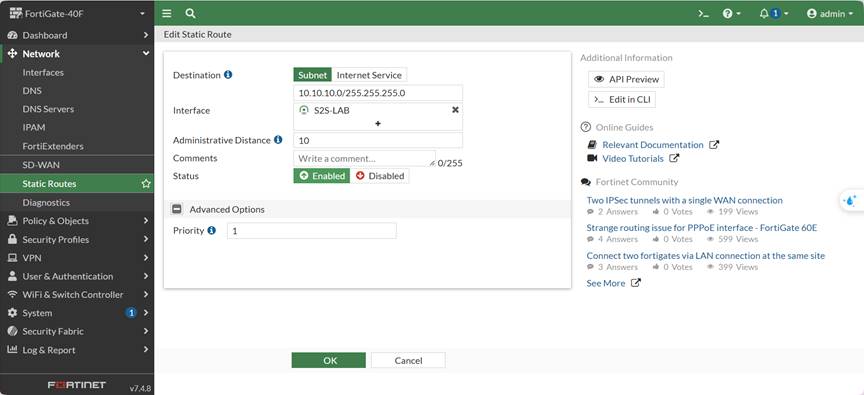
Route 1
| Parameter | Value |
|---|---|
| Destination | 10.10.10.0/24 |
| Interface | S2S-LAB |
| Gateway | 0.0.0.0 |
| Status | Enable |
Route 2
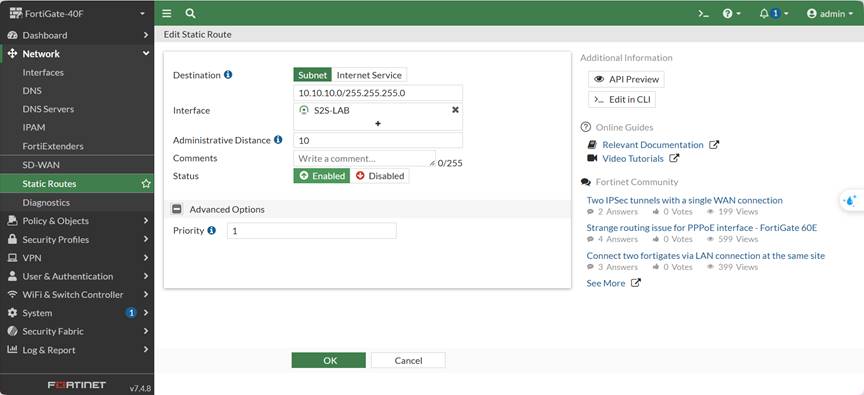
| Parameter | Value |
|---|---|
| Destination | 192.168.20.0/24 |
| Interface | S2S-LAB |
| Gateway | 0.0.0.0 |
| Status | Enable |
If the static route is missing → ping will never enter the VPN.
Policy 1 – LAN → VPN
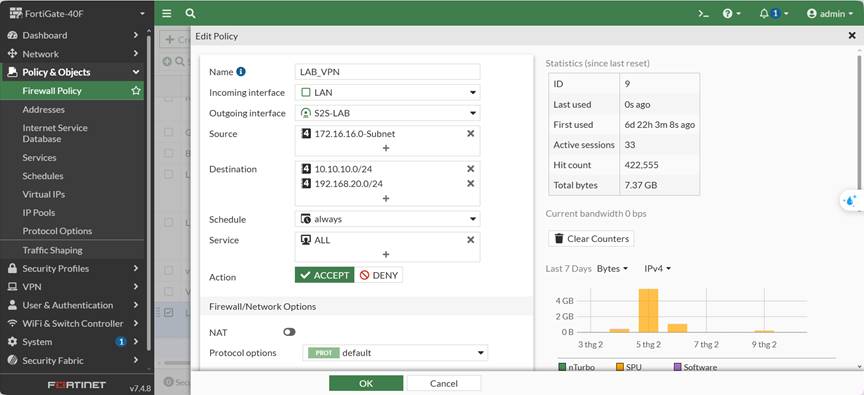
| Parameter | Value |
|---|---|
| Incoming Interface | LAN |
| Outgoing Interface | S2S-LAB |
| Source | 172.16.16.0/24 |
| Destination | 10.10.10.0/24, 192.168.20.0/24 |
| Service | ALL |
| Action | ACCEPT |
| NAT | Disable |
Policy 2 – VPN → LAN
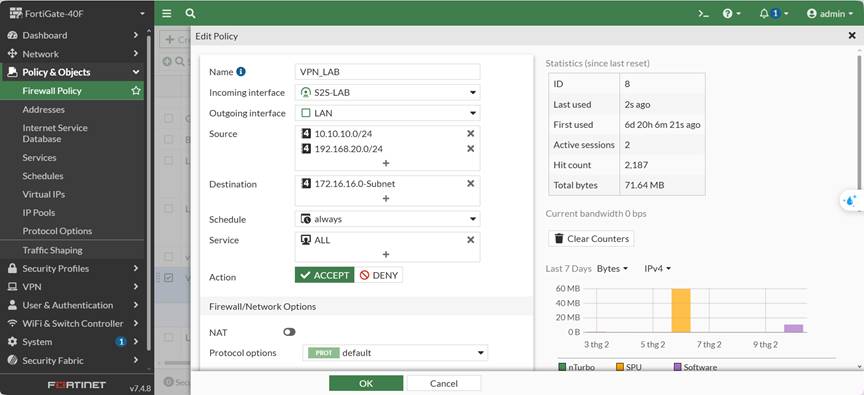
| Parameter | Value |
|---|---|
| Incoming Interface | S2S-LAB |
| Outgoing Interface | LAN |
| Source | 10.10.10.0/24, 192.168.20.0/24 |
| Destination | 172.16.16.0/24 |
| Service | ALL |
| Action | ACCEPT |
The VPN policy must be placed above the Internet policy.
Go to: Hosts and Services → Add
| Name | Type | Parameters |
|---|---|---|
| LAN_SOPHOS_10 | Network | IP: 10.10.10.0 / Subnet: 255.255.255.0 |
| LAN_SOPHOS_20 | Network | IP: 192.168.20.0 / Subnet: 255.255.255.0 |
| LAN_FORTI | Network | IP: 172.16.16.0 / Subnet: 255.255.255.0 |
Go to: SYSTEM > Profiles → IPsec Profiles → Add
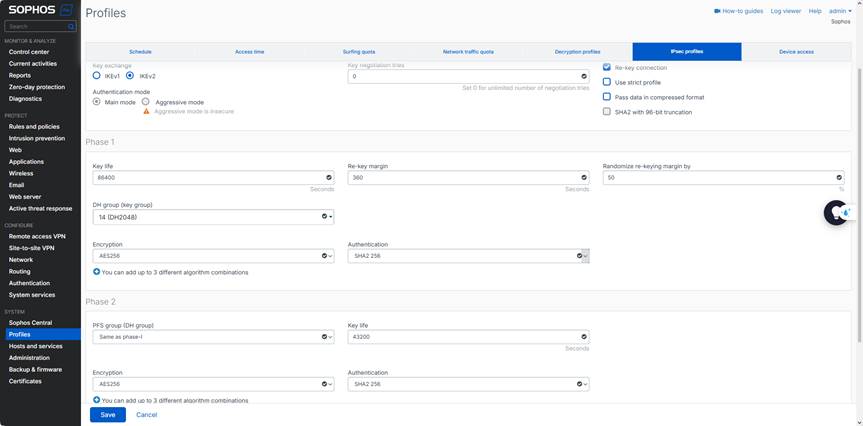
| Parameters | Value |
|---|---|
| Name | Fortinet-Vacif |
| IKE Version | IKEv2 |
| Encryption | AES256 |
| Authentication | SHA256 |
| DH Group | 14 |
Go to: CONFIGURE → Site-to-site VPN → IPsec → Add
General Settings
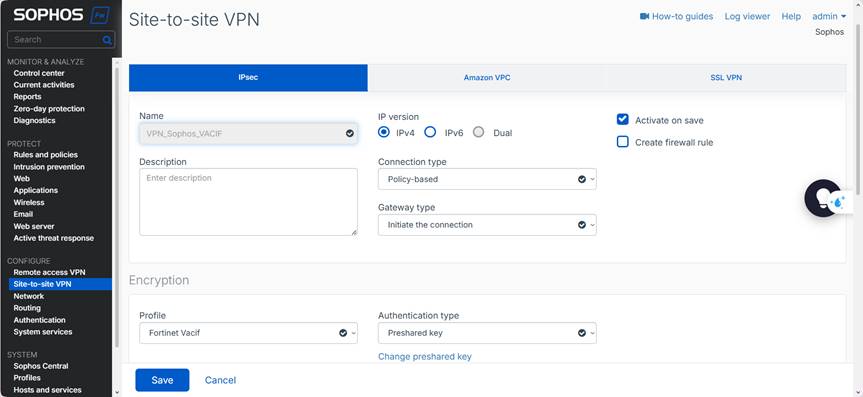
| Parameter | Value |
|---|---|
| Name | VPN_SOPHOS_VACIF |
| Connection Type | Policy-based |
| Gateway Type | Initiate the connection |
| Create firewall rule | Không chọn (tạo thủ công) |
Authentication
| Parameter | Value |
|---|---|
| Profile | Fortinet Vacif ( tạo ở bước trên ) |
| Authentication Type | Pre-shared Key |
| Pre-shared Key | FortiSophos@123 |
Gateway Settings
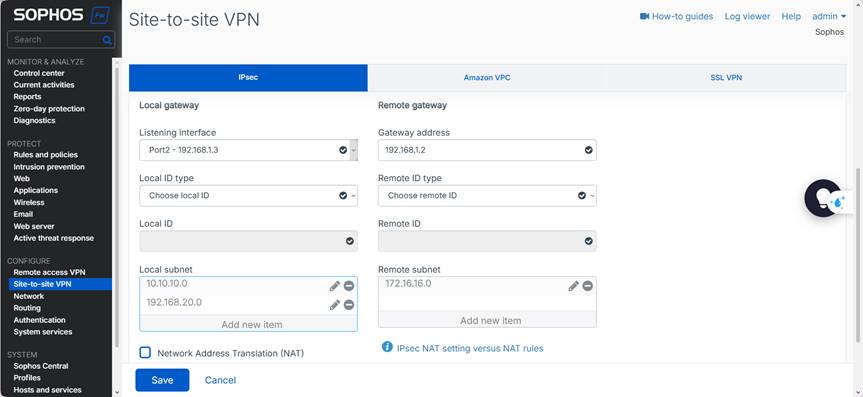
- Listening interface: Port 2 – 192.168.1.3
- Gateway address: 192.168.1.2 (WAN Fortinet)
- Local Subnet: 10.10.10.0/24 , 192.168.20.0/24
- Remote Subnet: 172.16.16.0/24
LAN → VPN
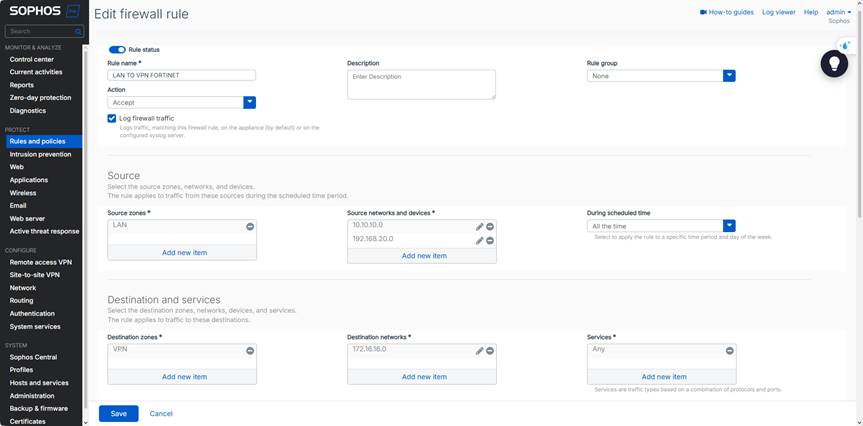
| Parameter | Value |
|---|---|
| Source Zone | LAN |
| Destination Zone | VPN |
| Source Network | 10.10.10.0/24, 192.168.20.0/24 |
| Destination Network | 172.16.16.0/24 |
| Action | Allow |
VPN → LAN
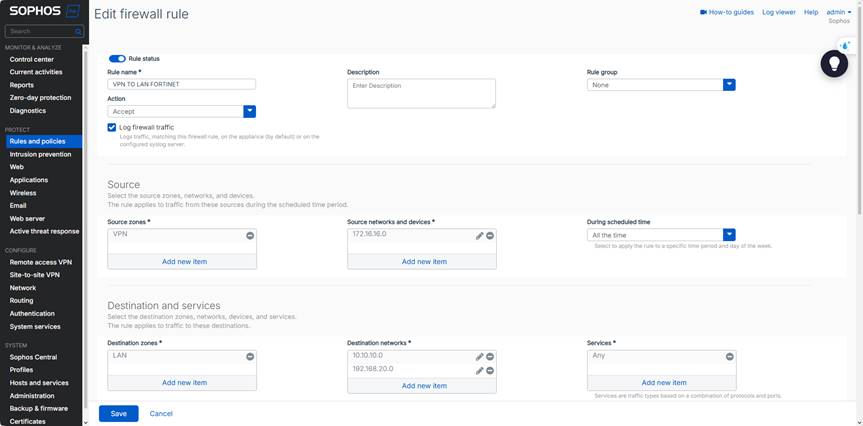
| Parameter | Value |
|---|---|
| Source Zone | VPN |
| Destination Zone | LAN |
| Source Network | 172.16.16.0/24 |
| Destination Network | 10.10.10.0/24, 192.168.20.0/24 |
| Action | Allow |
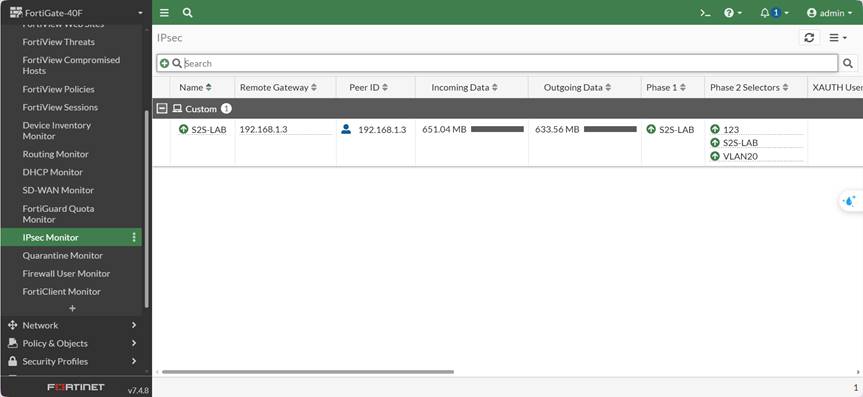
Sophos: VPN → IPsec Connections → Status: 🟢 Connected
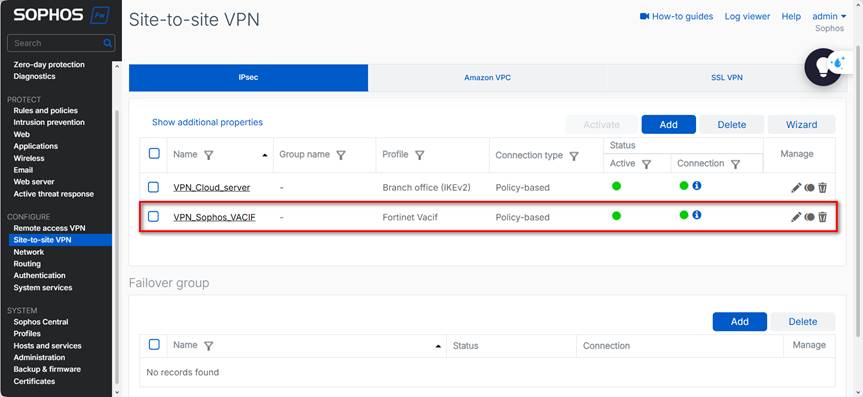
Fortinet: Monitor → IPsec Monitor → Tunnel: UP (Incoming / Outgoing Data present)
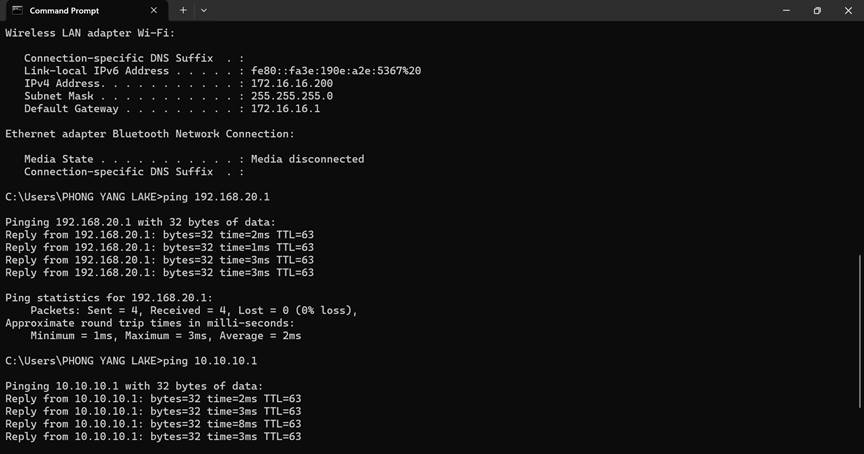
Test:
- 172.16.16.x → 10.10.10.x
- 172.16.16.x → 192.168.20.x
- Ensure system time is synchronized (NTP) to avoid IKEv2 errors caused by time mismatch.
- PSK, encryption algorithms, and DH groups must match on both sides — mismatches will cause Phase 1/2 failures.
- Disable NAT on policies entering the VPN; enabling NAT will alter the source and packets will not match the selector.
- Each Local/Remote subnet pair requires one selector (Phase 2). Do not combine multiple subnets if the device does not support it.
- If the tunnel is UP but ping does not work, check: Static Route, policy order, and the ARP/Route table on both sides.